How to configure MSDTC on Linux – SQL Server
MSSQL, SQL On Linux MSDTC, MSDTC configuration, SQL on Linux, SQL Server on LinuxDistributed transactions are enabled on SQL Server on Linux by introducing MSDTC and RPC endpoint mapper functionality within SQL Server. By default, RPC endpoint-mapping process listens on port 135 for incoming RPC requests and provides registered components information to remote requests. Remote requests can use the information returned by endpoint mapper to communicate with registered RPC components, such as MSDTC services. Please refer this page for more details on MSDTC.
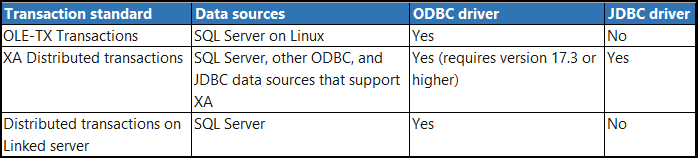
Supported transaction standards:
The following MSDTC configurations are supported:
Below are step by step process to enable MSDTC on SQL server on Linux environment.
Step#1: Configure RPC and MSDTC ports:
- Use mssql-conf to set the network.rpcport value to 13500.
sudo /opt/mssql/bin/mssql-conf set network.rpcport 13500- Set the distributedtransaction.servertcpport value to 51999.
sudo /opt/mssql/bin/mssql-conf set distributedtransaction.servertcpport 51999- Restart SQL Server
sudo systemctl restart mssql-serverStep#2: Configure Firewall:
Configure the firewall to allow communication on rpcport, servertcpport, and port 135. This enables MSDTC process to communicate externally to other transaction managers and coordinators.
sudo firewall-cmd --zone=public --add-port=51999/tcp --permanent
sudo firewall-cmd --zone=public --add-port=135/tcp --permanent
sudo firewall-cmd –reloadStep#3: Configure Port Routing:
Configure the Linux server routing table so that RPC communication on port 135 is redirected to SQL Server's network.rpcport
sudo firewall-cmd --permanent --add-forward-port=port=135:proto=tcp:toport=13500
sudo firewall-cmd –reloadHow useful was this post?
Click on a star to rate it!
Average rating 5 / 5. Vote count: 2
No votes so far! Be the first to rate this post.